Stop Losing Customers
To Problems
You Can’t See.
Soloprenero is a specialized digital architecture firm. We don’t guess why your business isn’t growing—we audit it. Using a 21-point technical scan, we generate a comprehensive Business Report Card that identifies the exact “money leaks” in your website architecture, local visibility, and online reputation. We find the gaps; you get the grades.
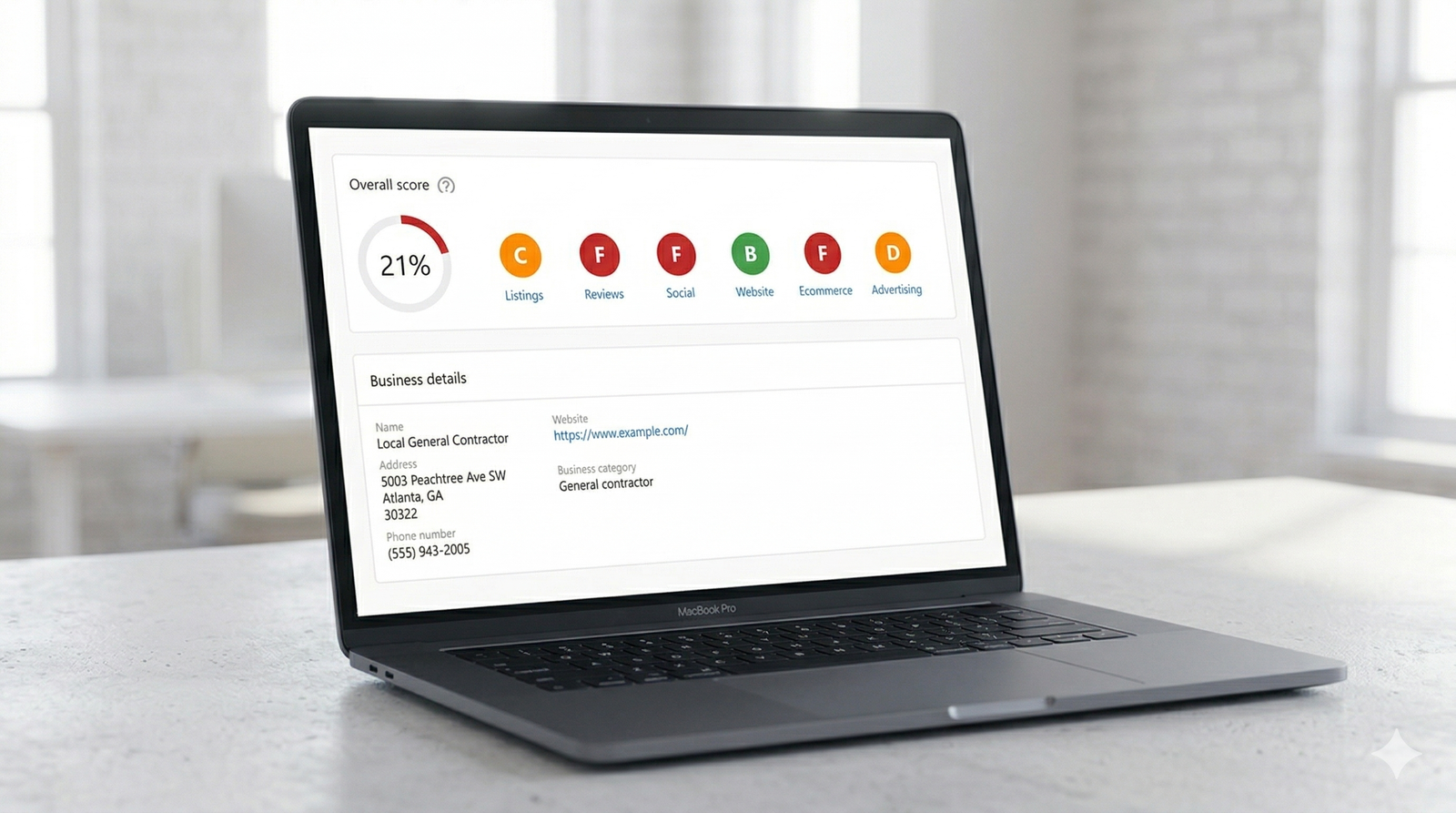
- Visibility & Search Authority: If a neighbor searches for your services, do they see your name or the guy down the street? We grade your local “findability” against your top competitors.
- Reputation & Social Proofing: We audit your online “word of mouth.” We’ll tell you if your reviews are an “A” or if they are failing to close the deal before the first call.
- Technical Architecture: A slow site is a locked door. We run a diagnostic on your mobile speed, lead-capture tracking, and hidden errors stopping conversions.
Request Priority Access
To maintain architectural accuracy, we only process one (1) complimentary Report Card per 24 hours.
Submit your site details to be considered for tomorrow’s priority selection. If selected, you will receive your objective A-F letter grades followed by a comprehensive technical breakdown of your results. No guesswork, just data.
STATUS: TODAY’S SLOT FILLED
Next Audit Selection: 24 Hours
Terms of Service
Last Updated:
01. Strategic Framework & Acceptance
These Terms of Service (“Framework”) govern the access to and utilization of the technical consultancy, digital infrastructure, and professional advisory services provided by Soloprenero. By interacting with our digital entry points or requesting a Technical Audit, you acknowledge and agree to operate within this defined professional perimeter.
02. Taxonomy of Technical Services
- Infrastructure Audits: Any “Tech Audit” or preliminary system assessment is provided as a high-level strategic roadmap. These outputs are intended for guidance and do not constitute a full system deployment or a guaranteed commercial outcome without an executed Statement of Work (SOW).
- Fractional CTO Advisory: Strategic direction provided under an advisory capacity is intended to optimize client-side decision-making. The final implementation and management of these strategies remain under the client’s operational authority unless otherwise specified in a service agreement.
03. Proprietary Logic & Intellectual Property
All architectural designs, specialized code snippets (including but not limited to Playwright automation scripts and QA protocols), systemic workflows, and brand assets contained within this ecosystem are the exclusive intellectual property of Soloprenero.
- Limited License: Clients are granted a non-exclusive license to utilize delivered logic for their internal business operations.
- Restricted Replication: Unauthorized redistribution, white-labeling, or commercial resale of Soloprenero’s proprietary “Silent Partner” methodology or automation frameworks is strictly prohibited.
04. Third-Party Ecosystem Dynamics
Soloprenero architects solutions that interface with global ecommerce, fulfillment, and hosting infrastructures.
- Platform Neutrality: We maintain a platform-agnostic stance to ensure the best technical fit for each mission.
- Liability Limitation: Soloprenero maintains no liability for the internal uptime, sudden policy shifts, API deprecations, or security vulnerabilities of third-party platforms. Our responsibility is limited to the engineering of the interface, not the maintenance of the external destination.
05. Client Responsibilities
For high-performance execution, the client must provide timely access to necessary systems and accurate business intelligence. Delays in data provision or system access may result in a reconfiguration of the deployment timeline.
06. Confidentiality & Protocol
We operate under a “Zero-Leak” philosophy. Any proprietary business intelligence, trade secrets, or project-specific data shared during an engagement is treated as strictly confidential. Formal Non-Disclosure Agreements (NDAs) are a standard requirement for all multi-phase infrastructure deployments and CTO engagements.
07. Professional Liability & Disclaimers
Soloprenero provides enterprise-grade technical strategy designed for rapid scale. However, we do not guarantee specific financial returns. We are not liable for:
- Force majeure events impacting global digital infrastructure.
- Data loss occurring on unmanaged or legacy client systems.
- Third-party hardware or software failures outside our direct cryptographic control.
08. Governing Jurisdiction
This Framework and any subsequent professional engagements shall be governed by and construed in accordance with the laws of the State of Georgia, USA. Any legal disputes shall be resolved exclusively within the jurisdiction of the courts located in Atlanta, GA.
09. Framework Modifications
We reserve the right to iterate upon these terms as our technical capabilities and service offerings evolve. Continued engagement with our systems constitutes acceptance of the current version of the Framework.
Privacy Policy
Last Updated:
01. Strategic Intent & Privacy by Design
At Soloprenero, we view data privacy as a critical component of system architecture. Our “Privacy by Design” philosophy ensures that data protection is integrated into every automated workflow and consulting engagement. This policy serves as a technical specification for how we acquire, process, and safeguard information within our ecosystem.
02. Taxonomy of Data Collection
We categorize the information we collect into three distinct tiers to maintain a minimal footprint:
- Identity Intelligence: Information explicitly provided by you during the inquiry or audit request phase (e.g., full name, professional email address, and business domain).
- Heuristic Telemetry: Diagnostic data automatically captured during your interaction with our digital infrastructure. This includes anonymized IP addresses, browser specifications, device hardware profiles, and navigation patterns.
- Project Intelligence: Proprietary data assets shared during high-level Fractional CTO engagements. This data is segregated and managed under project-specific security protocols and non-disclosure agreements (NDAs).
03. Methods of Data Acquisition
Data enters our system through two primary vectors:
- Direct Interaction: Information submitted via secure transmission forms for Technical Audits, system inquiries, or newsletter subscriptions.
- Automated Logging: We utilize industry-standard cookies and localized tracking technologies to monitor system health and optimize user experience. You may modulate these settings via your local browser environment.
04. Operational Use of Information
Your data is utilized exclusively for the optimization of our professional relationship:
- Service Delivery: Executing requested Technical Audits, infrastructure assessments, and strategic roadmaps.
- Communication Protocols: Distributing critical system updates, technical briefs, and deployment notifications.
- System Refinement: Analyzing diagnostic telemetry to harden our security layers and streamline automated workflows.
05. Third-Party Infrastructure Ecosystems
To maintain high-velocity service delivery, we utilize a vetted stack of enterprise-grade third-party infrastructure providers for CRM, secure hosting, and logistics fulfillment.
- Platform Agnosticism: We do not maintain exclusive allegiances to specific vendors; however, all partners are audited for compliance with global data protection frameworks (including GDPR, CCPA, and relevant local statutes).
- No Commercial Data Transfer: We do not sell, trade, or lease your personal data to external marketing entities. Data transfer is limited strictly to operational necessity.
06. Data Retention & Lifecycle Management
We adhere to a strict data lifecycle policy. Information is retained only as long as necessary to fulfill its primary operational objective or to meet statutory legal obligations. Once the utility of the data is exhausted, it is purged via secure cryptographic erasure.
07. Defensive Protocols & Security Architecture
As specialists in automated Quality Assurance and system reliability, we treat security as an end-to-end requirement.
- Encryption: All data in transit and at rest is protected by industry-standard encryption protocols.
- Zero-Trust Environment: We apply a Zero-Trust philosophy to our internal administrative access, ensuring that only verified entities can interact with project data.
08. Global Compliance & User Rights
Regardless of your geographic location, Soloprenero provides the following data rights:
- The Right to Inspect: You may request a summary of the data we hold regarding your professional profile.
- The Right to Rectify: You may update or correct any inaccuracies in your identity intelligence.
- The Right to Erasure: You may request the permanent deletion of your data from our active service environment, subject to legal retention requirements.
09. Policy Iterations
As our technical infrastructure evolves, this policy will be updated to reflect new security layers and service capabilities. We recommend periodic review of this document to stay aligned with our current deployment phase.
